leads4pass has updated Cisco 350-201 dumps issues! The latest 350-201 exam questions can help you pass the exam!
All questions are corrected to ensure authenticity and effectiveness! Download the leads4pass 350-201 VCE dumps or PDF dumps: https://www.leads4pass.com/350-201.html (Total Questions: 139 Q&A)
Cisco 350-201 Practice testing questions from Youtube
Latest Cisco 350-201 google drive
[PDF] Free Cisco 350-201 pdf dumps download from Google Drive: https://drive.google.com/file/d/18GMS9thcqcw2Bo26mGPicjh-1JmWZroU/
[Updated 2022]:https://drive.google.com/file/d/1AWESvo5Beac9z16xeX9pw-cyNhDM0Cnc/
Get more complete Cisco CCNP exam certification practice questions https://www.vcecert.com/cisco-dumps/
[Updated 2022] Latest Cisco 350-201 dumps exam questions Free sharing
Question 1:
Refer to the exhibit. A threat actor behind a single computer exploited a cloud-based application by sending multiple concurrent API requests. These requests made the application unresponsive. Which solution protects the application from being overloaded and ensures more equitable application access across the end-user community?
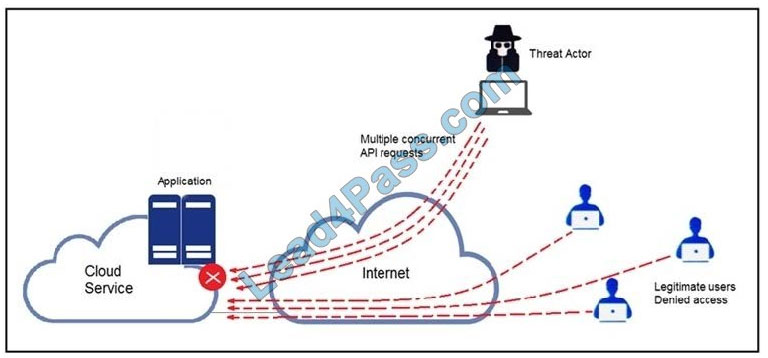
A. Limit the number of API calls that a single client is allowed to make
B. Add restrictions on the edge router on how often a single client can access the API
C. Reduce the amount of data that can be fetched from the total pool of active clients that call the API
D. Increase the application cache of the total pool of active clients that call the API
Correct Answer: A
Question 2:
A threat actor attacked an organization\’s Active Directory server from a remote location, and in a thirty-minute timeframe, stole the password for the administrator account and attempted to access 3 company servers. The threat actor successfully accessed the first server that contained sales data, but no files were downloaded. A second server was also accessed that contained marketing information and 11 files were downloaded. When the threat actor accessed the third server that contained corporate financial data, the session was disconnected, and the administrator\’s account was disabled.
Which activity triggered the behavior analytics tool?
A. accessing the Active Directory server
B. accessing the server with financial data
C. accessing multiple servers
D. downloading more than 10 files
Correct Answer: C
Question 3:
Refer to the exhibit. A security analyst needs to investigate a security incident involving several suspicious connections with a possible attacker. Which tool should the analyst use to identify the source IP of the offender?
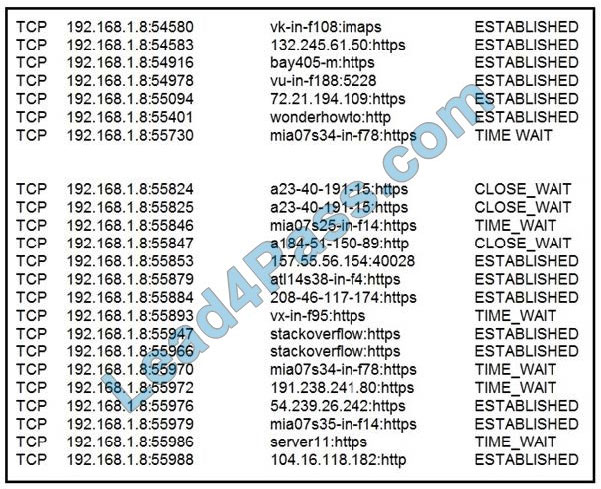
A. packet sniffer
B. malware analysis
C. SIEM
D. firewall manager
Correct Answer: A
Question 4:
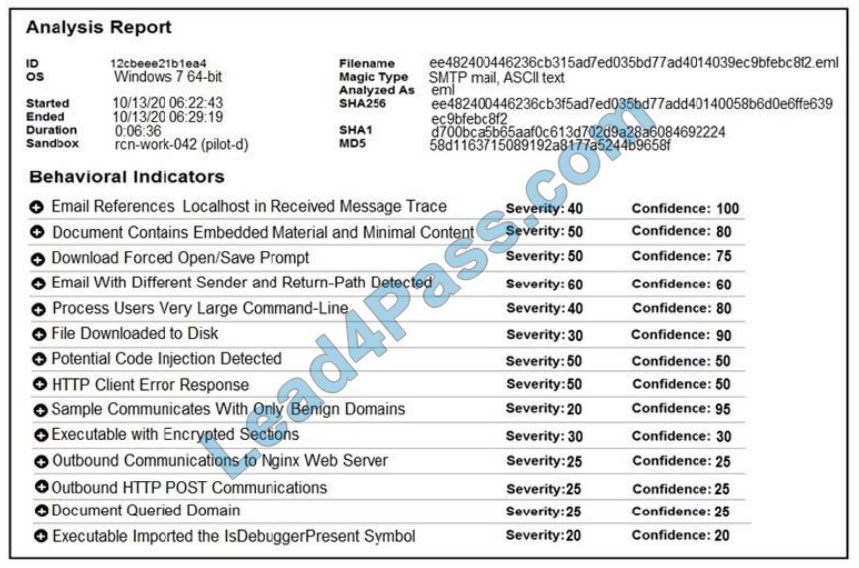
Refer to the exhibit. Cisco Advanced Malware Protection installed on an end-user desktop has automatically submitted a low prevalence file to the Threat Grid analysis engine for further analysis. What should be concluded from this report?
A. The prioritized behavioral indicators of compromise do not justify the execution of the “ransomware” because the scores do not indicate the likelihood of malicious ransomware.
B. The prioritized behavioral indicators of compromise do not justify the execution of the “ransomware” because the scores are high and do not indicate the likelihood of malicious ransomware.
C. The prioritized behavioral indicators of compromise justify the execution of the “ransomware” because the scores are high and indicate the likelihood that malicious ransomware has been detected.
D. The prioritized behavioral indicators of compromise justify the execution of the “ransomware” because the scores are low and indicate the likelihood that malicious ransomware has been detected.
Correct Answer: C
Question 5:
The physical security department received a report that an unauthorized person followed an authorized individual to enter a secured premises. The incident was documented and given to a security specialist to analyze. Which step should be taken at this stage?
A. Determine the assets to which the attacker has access
B. Identify assets the attacker handled or acquired
C. Change access controls to high-risk assets in the enterprise
D. Identify the movement of the attacker in the enterprise
Correct Answer: D
[Updated 2022] Get more up-to-date Cisco 350-201 exam questions and answers
The latest update of Cisco 350-201 exam questions and answers and official exam information tips
QUESTION 1:
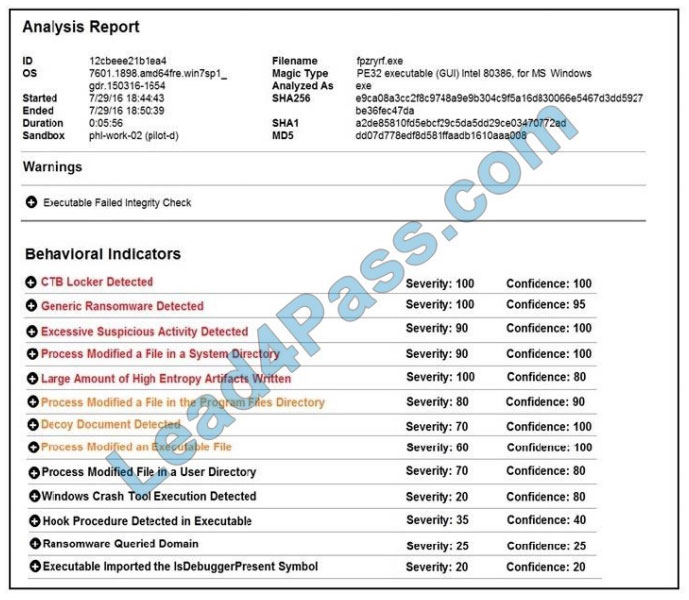
Refer to the exhibit. Cisco Advanced Malware Protection installed on an end-user desktop has automatically submitted a low prevalence file to the Threat Grid analysis engine for further analysis. What should be concluded from this report?
A. The prioritized behavioral indicators of compromise do not justify the execution of the “ransomware” because the scores do not indicate the likelihood of malicious ransomware.
B. The prioritized behavioral indicators of compromise do not justify the execution of the “ransomware” because the scores are high and do not indicate the likelihood of malicious ransomware.
C. The prioritized behavioral indicators of compromise justify the execution of the “ransomware” because the scores are high and indicate the likelihood that malicious ransomware has been detected.
D. The prioritized behavioral indicators of compromise justify the execution of the “ransomware” because the scores are low and indicate the likelihood that malicious ransomware has been detected.
Correct Answer: C
QUESTION 2:
Refer to the exhibit. Which command was executed in PowerShell to generate this log?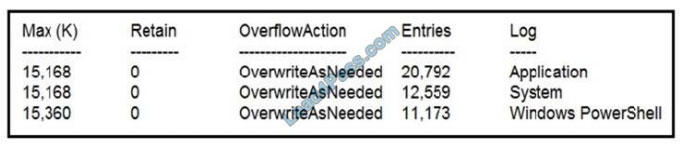
A. Get-EventLog -LogName*
B. Get-EventLog -List
C. Get-WinEvent -ListLog* -ComputerName localhost
D. Get-WinEvent -ListLog*
Correct Answer: A
Reference: https://lists.xymon.com/archive/2019-March/046125.html
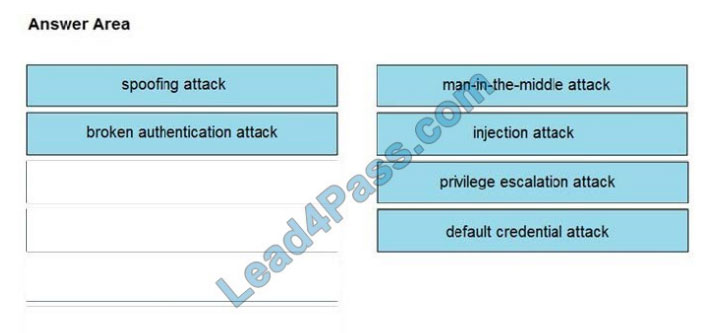
QUESTION 3:
DRAG-DROP
Drag and drop the threat from the left onto the scenario that introduces the threat on the right. Not all options are used.
Select and Place:
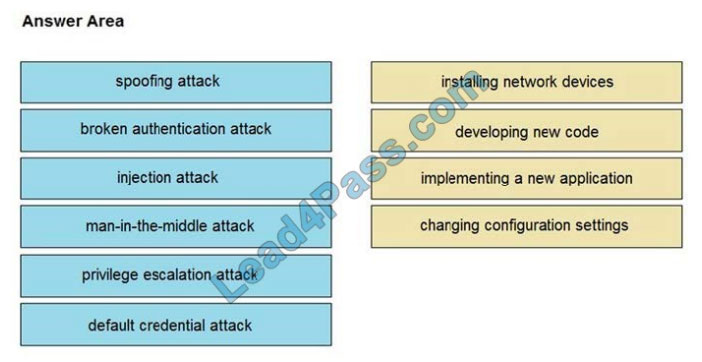
Correct Answer:
QUESTION 4:
A SOC analyst is notified by the network monitoring tool that there are unusual types of internal traffic on the IP subnet 103.861.2117.0/24. The analyst discovers unexplained encrypted data files on a computer system that belongs on that specific subnet.
What is the cause of the issue?
A. DDoS attack
B. phishing attack
C. virus outbreak
D. malware outbreak
Correct Answer: D
QUESTION 5:
Refer to the exhibit. Which asset has the highest risk value?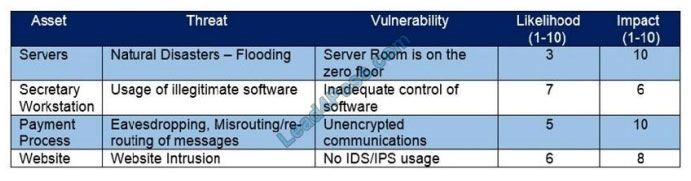
A. servers
B. website
C. payment process
D. secretary workstation
Correct Answer: C
QUESTION 6:
What is the principle of Infrastructure as Code?
A. System maintenance is delegated to software systems
B. Comprehensive initial designs support robust systems
C. Scripts and manual configurations work together to ensure repeatable routines
D. System downtime is grouped and scheduled across the infrastructure
Correct Answer: B
QUESTION 7:
An analyst is alerted to a malicious file hash. After analysis, the analyst determined that an internal workstation is communicating over port 80 with an external server and that the file hash is associated with Duqu malware. Which tactics, techniques, and procedures align with this analysis?
A. Command and Control, Application Layer Protocol, Duqu
B. Discovery, Remote Services: SMB/Windows Admin Shares, Duqu
C. Lateral Movement, Remote Services: SMB/Windows Admin Shares, Duqu
D. Discovery, System Network Configuration Discovery, Duqu
Correct Answer: A
QUESTION 8:
Refer to the exhibit. For IP 192.168.1.209, what are the risk level, activity, and next step?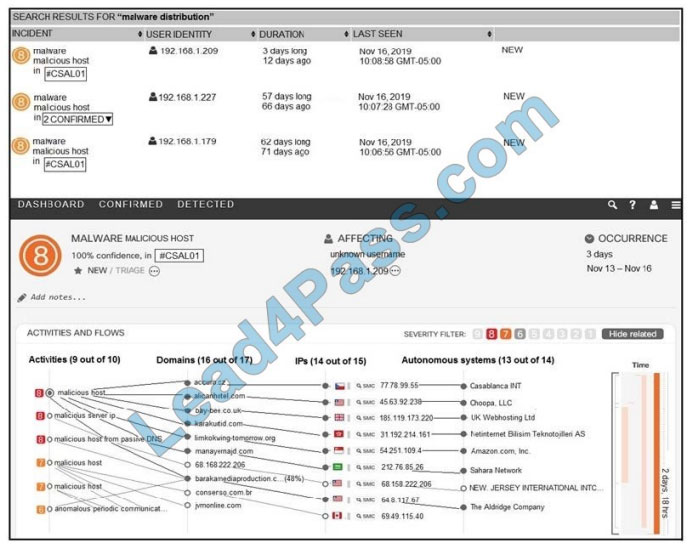
A. high-risk level, anomalous periodic communication, quarantine with antivirus
B. critical risk level, malicious server IP, run in a sandboxed environment
C. critical risk level, data exfiltration, isolate the device
D. high-risk level, malicious host, investigate further
Correct Answer: A
QUESTION 9:
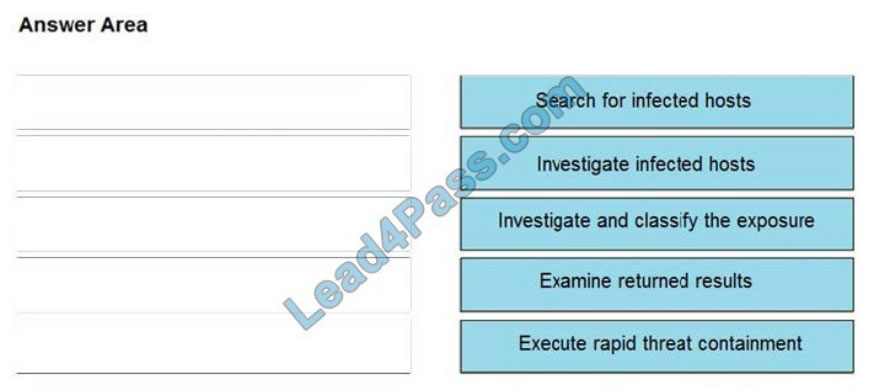
DRAG-DROP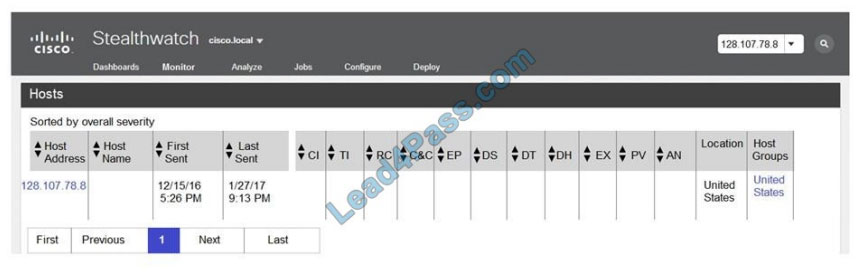
Refer to the exhibit. The Cisco Secure Network Analytics (Stealthwatch) console alerted with “New Malware Server Discovered” and the IOC indicates communication from an end-user desktop to a Zeus CandC Server. Drag and drop the actions that the analyst should take from the left into the order on the right to investigate and remediate this IOC.
Select and Place: 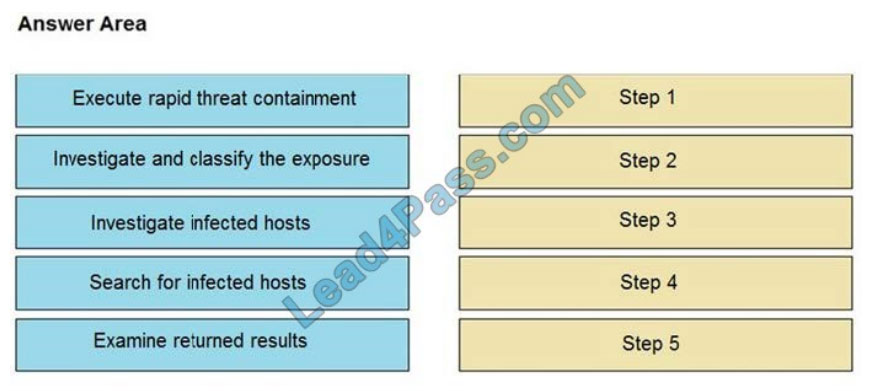
Correct Answer:
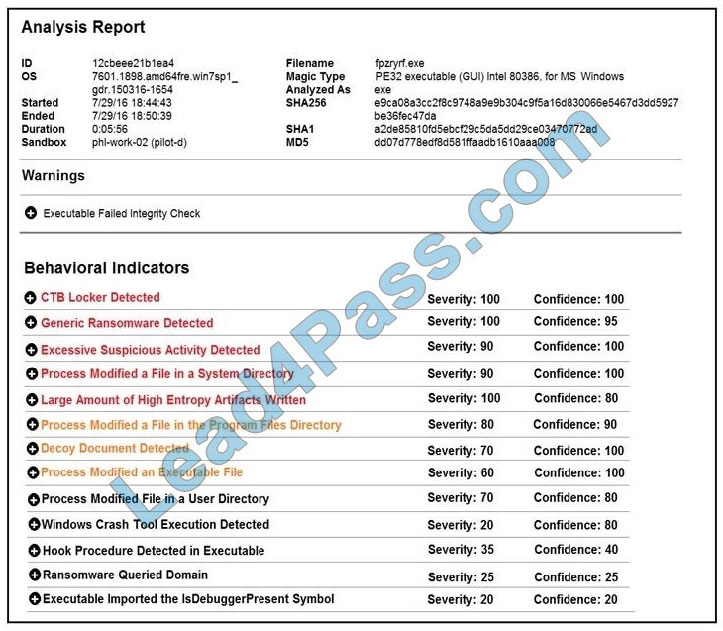
QUESTION 10:
Refer to the exhibit. Cisco Advanced Malware Protection installed on an end-user desktop automatically submitted a low prevalence file to the Threat Grid analysis engine. What should be concluded from this report?
A. Threat scores are high, malicious ransomware has been detected, and files have been modified
B. Threat scores are low, malicious ransomware has been detected, and files have been modified
C. Threat scores are high, malicious activity is detected, but files have not been modified
D. Threat scores are low and no malicious file activity is detected
Correct Answer: B
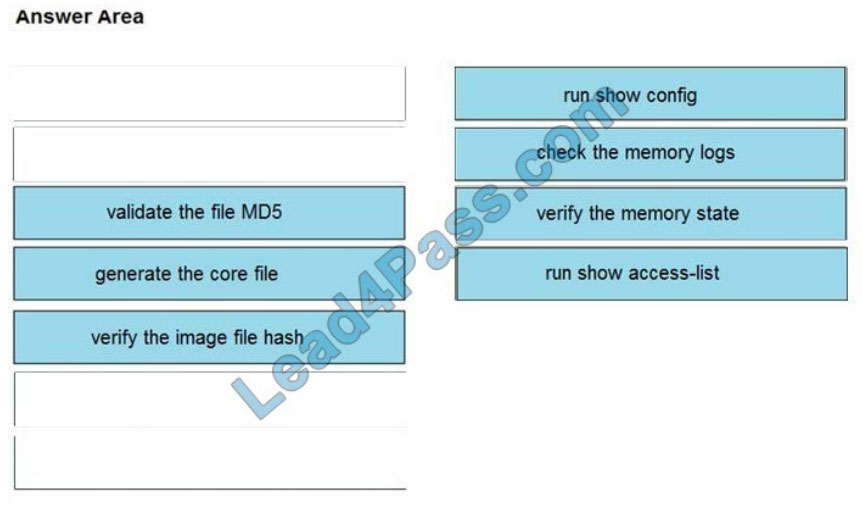
QUESTION 11:
DRAG-DROP
An organization lost connectivity to critical servers, and users cannot access business applications and internal websites. An engineer checks the network devices to investigate the outage and determines that all devices are functioning. Drag and drop the steps from the left into the sequence on the right to continue investigating this issue. Not all options are used.
Select and Place: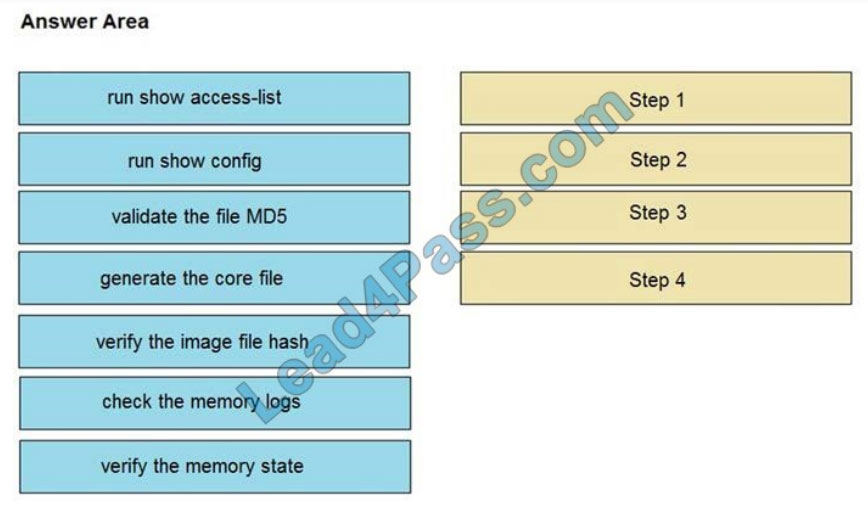
Correct Answer:
QUESTION 12:
An employee abused PowerShell commands and script interpreters, which lead to an indicator of compromise (IOC) trigger. The IOC event shows that a known malicious file has been executed, and there is an increased likelihood of a breach.
Which indicator generated this IOC event?
A. ExecutedMalware.ioc
B. Crossrider.ioc
C. ConnectToSuspiciousDomain.ioc
D. W32 AccesschkUtility.ioc
Correct Answer: D
QUESTION 13:
A threat actor used a phishing email to deliver a file with an embedded macro. The file was opened, and a remote code execution attack occurred in a company\\’s infrastructure. Which steps should an engineer take at the recovery stage?
A. Determine the systems involved and deploy available patches
B. Analyze event logs and restrict network access
C. Review access lists and require users to increase password complexity
D. Identify the attack vector and update the IDS signature list
Correct Answer: B
Summarize:
This blog shares the latest Cisco 350-201 exam dumps, and 350-201 exam questions and answers! 350-201 pdf, 350-201 exam video! You can also practice the test online! leads4pass is the industry leader!
Select https://www.leads4pass.com/350-201.html leads4pass 350-201 exams Pass Cisco 350-201 exams “Performing CyberOps Using Cisco Security Technologies (CBRCOR)”. Help you successfully pass the 350-201 exam.
[Q1-Q13 PDF] Free Cisco 350-201 pdf dumps download from Google Drive: https://drive.google.com/file/d/18GMS9thcqcw2Bo26mGPicjh-1JmWZroU/