High quality latest Cisco CCNA Cyber Ops 210-250 dumps exam real questions and answers free download from lead4pass. Practice for your Cisco CCNA Cyber Ops 210-250 exam with the help of lead4pass, at lead4pass you can find all the necessary things for yourself that will help you to pass Cisco 210-250 exam. “Understanding Cisco Cybersecurity Fundamentals” is the name of Cisco CCNA Cyber Ops https://www.leads4pass.com/210-250.html exam dumps which covers all the knowledge points of the real Cisco exam. You can download Cisco CCNA Cyber Ops 210-250 dumps pdf training material from lead4pass and pass the Cisco 210-250 exam in the first attempt. Cisco CCNA Cyber Ops 210-250 dumps exam preparation kit contains all the necessary 210-250 questions that you need to know.
【Latest Cisco 210-250 dumps pdf materials from google drive】: https://drive.google.com/open?id=0B_7qiYkH83VRaF8zb0JFVmRVclU
【Latest Cisco 210-255 dumps pdf materials from google drive】: https://drive.google.com/open?id=0B_7qiYkH83VRTTJsYkV3c2xZb2s
Vendor: Cisco
Certifications: CCNA Cyber Ops
Exam Name: Understanding Cisco Cybersecurity Fundamentals
Exam Code: 210-250
Total Questions: 80 Q&As
New Cisco CCNA Cyber Ops 210-250 Dumps Exam Real Questions And Answers (11-50)
QUESTION 11
Which information security property is supported by encryption?
A. sustainability
B. integrity
C. confidentiality
D. availability
Correct Answer: C
QUESTION 12
Which term describes the act of a user, without authority or permission, obtaining rights on a system, beyond what were assigned?
A. authentication tunneling
B. administrative abuse
C. rights exploitation
D. privilege escalation
Correct Answer: D
QUESTION 13
Which definition of the IIS Log Parser tool is true?
A. a logging module for IIS that allows you to log to a database
B. a data source control to connect to your data source
C. a powerful, versatile tool that makes it possible to run SQL-like queries against log flies
D. a powerful versatile tool that verifies the integrity of the log files
Correct Answer: C
QUESTION 14
What are the advantages of a full-duplex transmission mode compared to half-duplex mode? (Select all that apply.)
A. Each station can transmit and receive at the same time.
B. It avoids collisions.
C. It makes use of backoff time.
D. It uses a collision avoidance algorithm to transmit.
Correct Answer: AB
QUESTION 15
Which term represents the chronological record of how evidence was collected- analyzed, preserved, and transferred?
A. chain of evidence
B. evidence chronology
C. chain of custody
D. record of safekeeping
Correct Answer: C
QUESTION 16
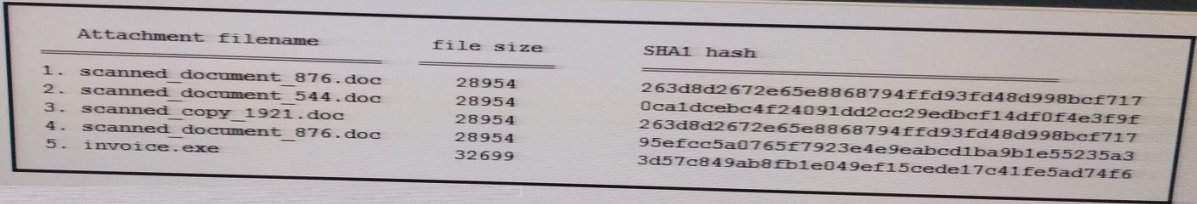
Refer to the exhibit. During an analysis this list of email attachments is found. 210-250 dumps Which files contain the same content?
A. 1 and 4
B. 3 and 4
C. 1 and 3
D. 1 and 2
Correct Answer: C
QUESTION 17
In which case should an employee return his laptop to the organization?
A. When moving to a different role
B. Upon termination of the employment
C. As described in the asset return policy
D. When the laptop is end of lease
Correct Answer: C
QUESTION 18
A firewall requires deep packet inspection to evaluate which layer?
A. application
B. Internet
C. link
D. transport
Correct Answer: A
QUESTION 19
Which event occurs when a signature-based IDS encounters network traffic that triggers an alert?
A. connection event
B. endpoint event
C. NetFlow event
D. intrusion event
Correct Answer: D
QUESTION 20
Which type of attack occurs when an attacker is successful in eavesdropping on a conversation between two IPS phones?
A. replay
B. man-in-the-middle
C. dictionary
D. known-plaintext
Correct Answer: B
QUESTION 21
Which situation indicates application-level white listing?
A. Allow everything and deny specific executable files.
B. Allow specific executable files and deny specific executable files.
C. Writing current application attacks on a whiteboard daily.
D. Allow specific files and deny everything else.
Correct Answer: B
QUESTION 22
Which definition of an antivirus program is true?
A. program used to detect and remove unwanted malicious software from the system
B. program that provides real time analysis of security alerts generated by network hardware and application
C. program that scans a running application for vulnerabilities
D. rules that allow network traffic to go in and out
Correct Answer: A
QUESTION 23
Which of the following is true about heuristic-based algorithms?
A. Heuristic-based algorithms may require fine tuning to adapt to network traffic and minimize the possibility of false positives.
B. Heuristic-based algorithms do not require fine tuning.
C. Heuristic-based algorithms support advanced malware protection.
D. Heuristic-based algorithms provide capabilities for the automation of IPS signature creation and tuning.
Correct Answer: A
QUESTION 24
Which security principle states that more than one person is required to perform a critical task?
A. due diligence
B. separation of duties
C. need to know
D. least privilege
Correct Answer: B
QUESTION 25
Which tool is commonly used by threat actors on a webpage to take advantage of the software vulnerabilities of a system to spread malware? 210-250 dumps
A. exploit kit
B. root kit
C. vulnerability kit
D. script kiddie kit
Correct Answer: A
QUESTION 26
If a web server accepts input from the user and passes it to a bash shell, to which attack method is it vulnerable?
A. input validation
B. hash collision
C. command injection
D. integer overflow
Correct Answer: C
QUESTION 27
Based on which statement does the discretionary access control security model grant or restrict access ?
A. discretion of the system administrator
B. security policy defined by the owner of an object
C. security policy defined by the system administrator
D. role of a user within an organization
Correct Answer: B
QUESTION 28
Which definition of the virtual address space for a Windows process is true?
A. actual physical location of an object in memory
B. set of virtual memory addresses that it can use
C. set of pages that are currently resident in physical memory
D. system-level memory protection feature that is built into the operating system
Correct Answer: B
QUESTION 29
Which statement about digitally signing a document is true?
A. The document is hashed and then the document is encrypted with the private key.
B. The document is hashed and then the hash is encrypted with the private key.
C. The document is encrypted and then the document is hashed with the public key
D. The document is hashed and then the document is encrypted with the public key.
Correct Answer: B
QUESTION 30
You must create a vulnerability management framework. Which main purpose of this framework is true?
A. Conduct vulnerability scans on the network.
B. Manage a list of reported vulnerabilities.
C. Identify remove and mitigate system vulnerabilities.
D. Detect and remove vulnerabilities in source code.
Correct Answer: B
QUESTION 31
Which definition of a process in Windows is true?
A. running program
B. unit of execution that must be manually scheduled by the application
C. database that stores low-level settings for the OS and for certain applications
D. basic unit to which the operating system allocates processor time
Correct Answer: A
QUESTION 32
According to the attribute-based access control (ABAC) model, what is the subject location considered?
A. Part of the environmental attributes
B. Part of the object attributes
C. Part of the access control attributes
D. None of the above
Correct Answer: A
QUESTION 33
Which term represents a potential danger that could take advantage of a weakness in a system?
A. vulnerability
B. risk
C. threat
D. exploit
Correct Answer: B
QUESTION 34
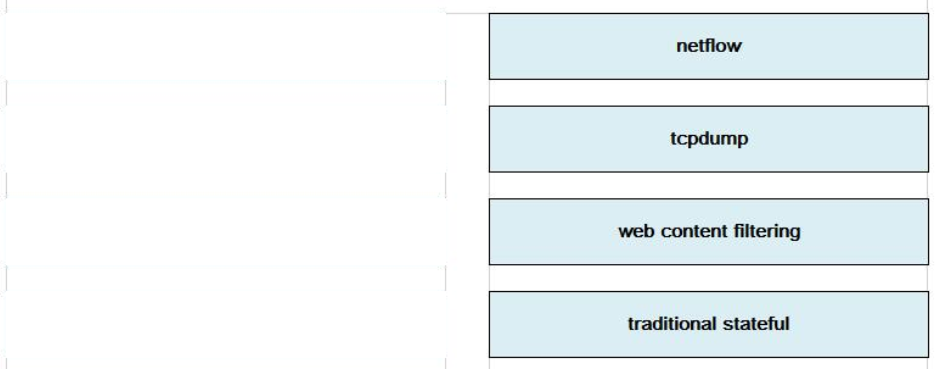
DRAG DROP
Drag the technology on the left to the data type the technology provides on the right.
Select and Place:
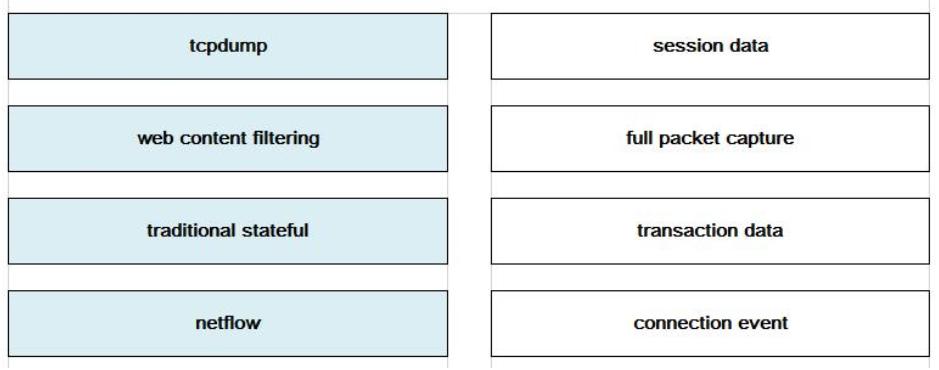
Correct Answer:
QUESTION 35
Which two services define cloud networks? (Choose two.)
A. Infrastructure as a Service
B. Platform as a Service
C. Security as a Service
D. Compute as a Service
E. Tenancy as a Service
Correct Answer: AB
QUESTION 36
You have implemented a Sourcefire IPS and configured it to block certain addresses utilizing Security Intelligence IP Address Reputation. 210-250 dumps A user calls and is not able to access a certain IP address. What action can you take to allow the user access to the IP address?
A. Create a whitelist and add the appropriate IP address to allow the traffic.
B. Create a custom blacklist to allow the traffic.
C. Create a user based access control rule to allow the traffic.
D. Create a network based access control rule to allow the traffic.
E. Create a rule to bypass inspection to allow the traffic.
Correct Answer: A
QUESTION 37
What is a benefit of a web application firewall?
A. It blocks known vulnerabilities without patching applications.
B. It simplifies troubleshooting.
C. It accelerates web traffic.
D. It supports all networking protocols.
Correct Answer: A
QUESTION 38
A data breach has occurred and your company database has been copied. Which
security principle has been violated?
A. confidentiality
B. availability
C. access
D. control
Correct Answer: A
QUESTION 39
A proxy firewall protects against which type of attack?
A. cross-site scripting attack
B. worm traffic
C. port scanning
D. DDoS attacks
Correct Answer: A
QUESTION 40
What are purposes of the Internet Key Exchange in an IPsec VPN? (Choose two.)
A. The Internet Key Exchange protocol establishes security associations
B. The Internet Key Exchange protocol provides data confidentiality
C. The Internet Key Exchange protocol provides replay detection
D. The Internet Key Exchange protocol is responsible for mutual authentication
Correct Answer: AD
QUESTION 41
Which two protocols are used for email (Choose two )
A. NTP
B. DNS
C. HTTP
D. IMAP
E. SMTP
Correct Answer: DE
QUESTION 42
At which OSI layer does a router typically operate?
A. Transport
B. Network
C. Data link
D. Application
Correct Answer: B
QUESTION 43
While viewing packet capture data, you notice that one IP is sending and receiving traffic for multiple devices by modifying the IP header, Which option is making this behavior possible?
A. TOR
B. NAT
C. encapsulation
D. tunneling
Correct Answer: B
QUESTION 44
Which option is a purpose of port scanning?
A. Identify the Internet Protocol of the target system.
B. Determine if the network is up or down
C. Identify which ports and services are open on the target host.
D. Identify legitimate users of a system.
Correct Answer: C
QUESTION 45
An intrusion detection system begins receiving an abnormally high volume of scanning from numerous sources. Which evasion technique does this attempt indicate?
A. traffic fragmentation
B. resource exhaustion
C. timing attack
D. tunneling
Correct Answer: B
QUESTION 46
Which two activities are examples of social engineering? (Choose two)
A. receiving call from the IT department asking you to verify your username/password to maintain the account
B. receiving an invite to your department’s weekly WebEx meeting
C. sending a verbal request to an administrator to change the password to the account of a user the administrator does know
D. receiving an email from MR requesting that you visit the secure HR website and update your contract information
E. receiving an unexpected email from an unknown person with an uncharacteristic attachment from someone in the same company
Correct Answer: AC
QUESTION 47
Cisco pxGrid has a unified framework with an open API designed in a hub-and-spoke architecture. 210-250 dumps pxGrid is used to enable the sharing of contextual-based information from which devices?
A. From a Cisco ASA to the Cisco OpenDNS service
B. From a Cisco ASA to the Cisco WSA
C. From a Cisco ASA to the Cisco FMC
D. From a Cisco ISE session directory to other policy network systems, such as Cisco IOS devices and the Cisco ASA
Correct Answer: D
QUESTION 48
Which definition of a daemon on Linux is true?
A. error check right after the call to fork a process
B. new process created by duplicating the calling process
C. program that runs unobtrusively in the background
D. set of basic CPU instructions
Correct Answer: C
QUESTION 49
A user reports difficulties accessing certain external web pages, When examining traffic to and from the external domain in full packet captures, you notice many SYNs that have the same sequence number, source, and destination IP address, but have different payloads.
Which problem is a possible explanation of this situation?
A. insufficient network resources
B. failure of full packet capture solution
C. misconfiguration of web filter
D. TCP injection
Correct Answer: D
QUESTION 50
Which definition describes the main purpose of a Security Information and Event Management solution ?
A. a database that collects and categorizes indicators of compromise to evaluate and search for potential security threats
B. a monitoring interface that manages firewall access control lists for duplicate firewall filtering
C. a relay server or device that collects then forwards event logs to another log collection device
D. a security product that collects, normalizes, and correlates event log data to provide holistic views of the security posture
Correct Answer: D
Useful latest Cisco CCNA Cyber Ops 210-250 dumps exam practice files and study guides in PDF format free download from lead4pass. The best and most updated latest Cisco CCNA Cyber Ops https://www.leads4pass.com/210-250.html dumps pdf training resources which are the best for clearing 210-250 exam test, and to get certified by Cisco CCNA Cyber Ops. Download Cisco CCNA Cyber Ops 210-250 dumps exam questions and verified answers. 100% passing guarantee and full refund in case of failure.
Best Cisco CCNA Cyber Ops 210-250 dumps vce youtube: https://youtu.be/YF5kWehwKzc
The Following Are Some Reviews From Our Customers:
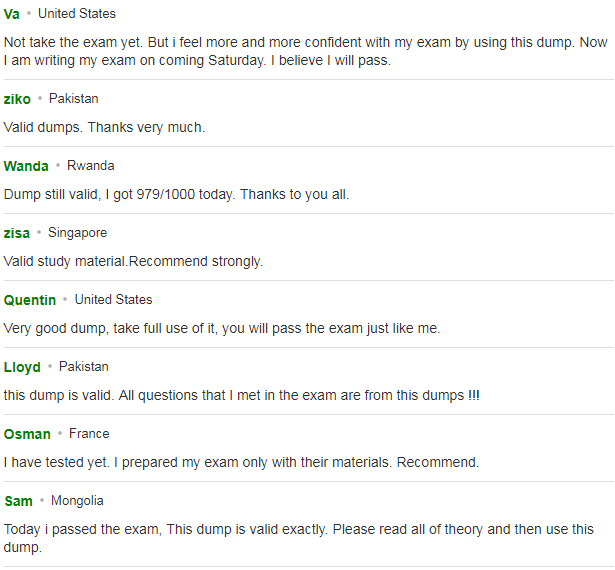
You can click here to have a review about us: https://www.resellerratings.com/store/lead4pass
Why Select Lead4pass?
Lead4pass is the best site for providing online preparation material for 210-250 exam. Get your Cisco CCNA Cyber Ops 210-250 exam prep questions in form of 210-250 PDF. Other brands started earlier, but the questions are outdated and the price is relatively expensive. Lead4pass provide the latest real and cheapest practice questions and answers, help you pass the exam easily at first try.
